Cloud computing security: These two Microsoft tools can help you battle shadow IT
CloudFinding what cloud services employees are using is half the battle–integrating Microsoft Cloud App Security and Defender Advanced Threat Protection lets you track, block, or audit cloud app usage.
Shadow IT used to mean someone writing Excel macros or setting up an unofficial file server for their team. Now, putting AWS and Salesforce subscriptions on the company credit card or using Dropbox to share documents with suppliers and partners is just the tip of the iceberg. The average enterprise has over 1,500 cloud apps in use, most of them not provisioned by the IT team, and is uploading more than 80GB a month to cloud services from within the business.
There are various tools that promise to detect cloud services in use inside your network, usually by scanning network traffic and checking firewall logs (although services like Zylo plug into financial systems to find SaaS subscriptions that departments are buying directly without going through IT). Not only is that cumbersome and likely to impact network speed, but it doesn’t help with remote users: you can only detect and block web applications by sending everyone through your corporate network — something that will be both unpopular and hard to enforce.
More about Windows
You get more control by analysing and controlling cloud app usage on the device directly. Microsoft Cloud App Security (MCAS, a Cloud Application Service Broker, which is itself a cloud service) now includes a shadow IT discovery tool that integrates with Defender ATP to discover cloud app and service usage on any managed device. Defender already monitors what processes are running and what files are being opened as it checks for malware, and that same information lets it report back on what cloud services are being used. It’s an automated process that creates a catalog of cloud apps that are in use, by which users and on which devices, with security and compliance risk scores for each app.
But because MCAS is integrated with Defender, you get the option to block and whitelist apps directly on the device. That works for all devices, not just the ones on the corporate network — and it even lets you enforce read-only access to your corporate resources for external users like suppliers and partners.
Defender ATP can look at the labels you apply with Azure Information Protection, so you can tell when data tagged as sensitive or confidential is being sent to a cloud service (or if files have been downloaded and stored on a device) — in real time, or later on, even if that device is no longer connected for you to scan or available for you to look at physically. Niv Goldenberg, principal group PM manager for cloud security, compares it to a flight recorder: the data is stored for six months in your cloud tenant, so you can go back and audit which files were accessed and what happened to the data if you need to do an investigation, which is an additional layer of protection even for approved cloud applications.
Once you find shadow IT in use you might block it, but you might also just keep an eye on it.
” data-credit=”Image: Microsoft” rel=”noopener noreferrer nofollow”> Once you find shadow IT in use you might block it, but you might also just keep an eye on it. Image: Microsoft 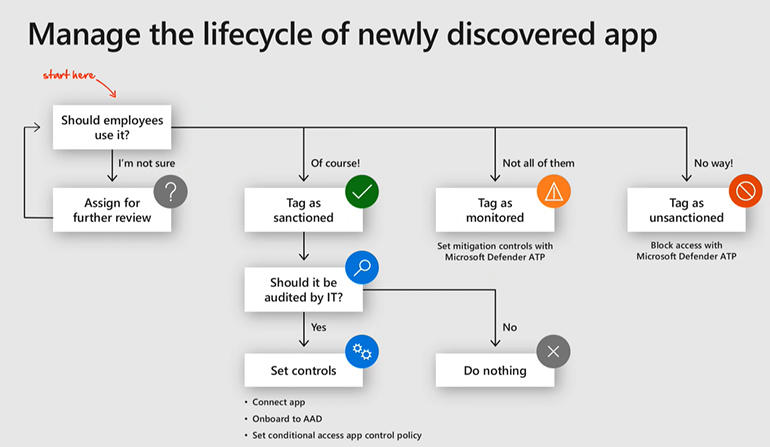
Cloud app reputation
The idea is to give organisations back the visibility and control over users and data that they lost when SaaS services arrived, Goldenberg told TechRepublic. “If I want to start using a new application, all I need to do is open my browser and type in a URL and I’m using an application that the IT department probably isn’t familiar with and doesn’t have any visibility or control over. Knowing what applications employees are using is one thing, but before you can decide if this is an application I want to encourage employees to use, or an application that I want to block, you need to know whether the application is secure enough. Based on the metrics we see of our customers, typically organisations use more than 1,500 cloud applications and there’s no way an IT admin knows all these applications and how secure they are.”
Shadow IT detection is easy to set up from within the portal where you manage Defender ATP.
” data-credit=”Image: Microsoft” rel=”noopener noreferrer nofollow”> Shadow IT detection is easy to set up from within the portal where you manage Defender ATP. Image: Microsoft 
Getting an audit of even official and approved apps that are in use is often a slow and tedious process, so just being able to see so quickly what cloud apps are being used is handy. But the security and compliance ratings in MCAS also help you understand how cloud services use and protect data, Goldenberg says. “Which of my data goes to the cloud? How is the data stored? Does it encrypt data at rest? Do I have sensitive files that are now publicly shared Is all my data, labelled and protected accurately? What is the risk am I exposing myself to as an organisation when someone uses this application?”
SEE: Windows 10: A cheat sheet (TechRepublic)
Some of that information is gathered through Microsoft’s automated tools, and by the company’s security researchers who look at new vulnerabilities and new compliance regulations like GDPR or the new California Consumer Privacy Act (CCPA). As a cloud service, MCAS will see new applications being accessed by customers at scale. “We see new URLs and new IPs and we can tell if this is a new application, a new signature for an existing application or something that’s not actually a cloud application,” says Goldenberg. Software vendors can also submit details and customers can ask Microsoft to check a service and rank it (both of those happen within two business days).
You can filter the list of applications by category or drill into the details that make up the overall risk score, down to whether it uses TLS and secure HTTP connections, how often it’s patched, what the data usage policy of the service is and who it’s owned by.
MCAS shows how many users are using how many different applications.
” data-credit=”Image: Microsoft” rel=”noopener noreferrer nofollow”> MCAS shows how many users are using how many different applications. Image: Microsoft 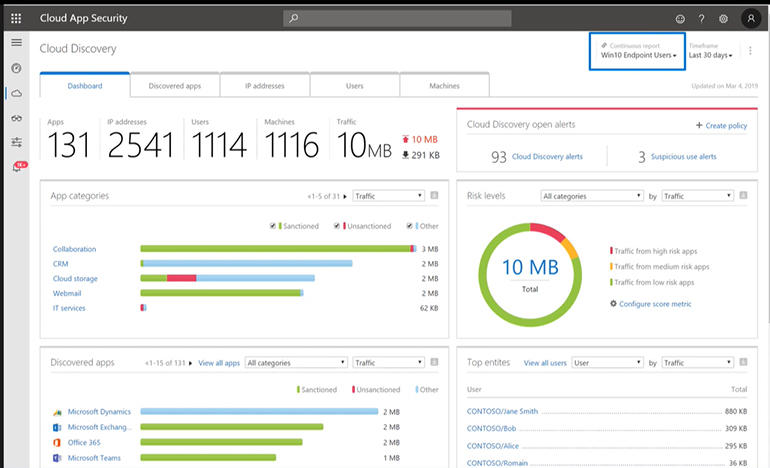
Dashboards show which applications are used and how widely, and what percentage of usage is approved applications versus shadow IT. You’ll also get an alert if vulnerabilities are found in cloud apps that your employees are using.
The Defender information is integrated here too, so you can drill down to individual users, devices and IP addresses and see the volume of data being uploaded or downloaded through the application. “If you see lots of traffic going to a risky application, you can pin down the specific machine initiating this traffic,” Goldenberg says. You can also see if users have different application behaviour on different devices, which might be suspicious — or might tell you that the official app you want everyone to use is just too slow on older desktops, making employees work around it.
With so many cloud services available, the security and compliance ratings are very useful.
” data-credit=”Image: Microsoft” rel=”noopener noreferrer nofollow”> With so many cloud services available, the security and compliance ratings are very useful. Image: Microsoft 
Drill in and see the details of why a cloud app gets the security and compliance ranking it does.
” data-credit=”Image: Microsoft” rel=”noopener noreferrer nofollow”> Drill in and see the details of why a cloud app gets the security and compliance ranking it does. Image: Microsoft 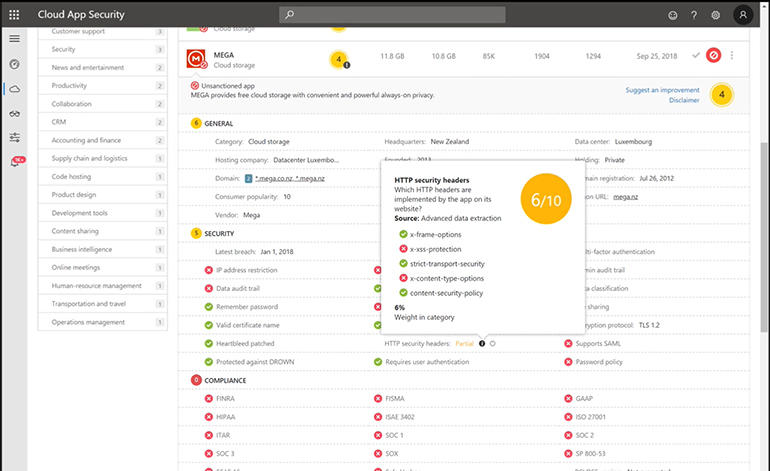
App governance and lifecycles
Don’t think about shadow IT in terms of what you can block, but think about how you can enable employees to safely adopt applications. “You can avoid shadow IT if you block any access to the internet,” says Goldenberg, adding that it’s hardly practical. Instead, MCAS lets you analyse what cloud applications are being used so you can understand why employees are using shadow IT.
“In most cases it’s because they have a business need that’s not met by the current solutions the IT department provides them with,” says Goldenberg. If employees don’t have a good way to share large files, they turn to services like WeTransfer or ShareFile. “Sometimes you see very enthusiastic information workers that just want to make the best presentation and they go to an online presentation tool that makes very nice presentations. But they don’t read the small print in the terms of usage that says all the content they upload to the service the provider can share with whoever they want. Or you see people using PDF converters online because it’s so easy but then they take a business-critical or a business-confidential document and copy paste it into one of those cloud services.”
Track how many users have seen warnings or been blocked from using a cloud service.
” data-credit=”Image: Microsoft” rel=”noopener noreferrer nofollow”> Track how many users have seen warnings or been blocked from using a cloud service. Image: Microsoft 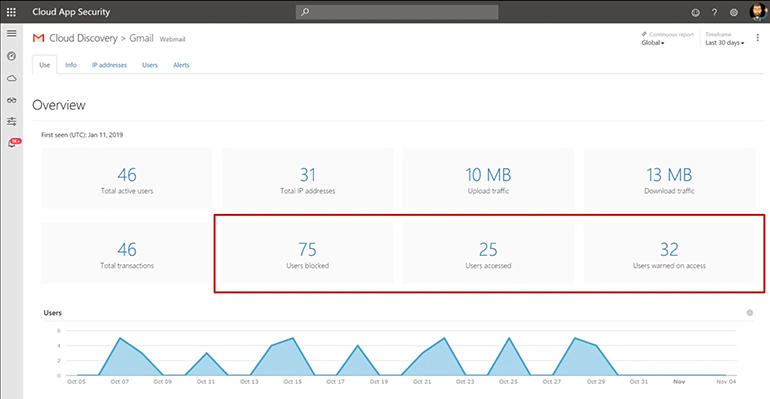
Just blocking a service like that without explaining the problem to employees, or giving them a safe alternative, is setting yourself up for an unending game of ‘whack-a-mole’, because you’ll just have to keep blocking more services. Managing shadow IT is an ongoing process because new applications are always coming along, people change the way they use the cloud over time, and previously approved apps may need to be deprecated later.
Start by tracking what cloud applications are being used, whether they’re the ones you expect, and how they fit in with your application governance policies — which might include temporarily blocking applications while they go through legal review or technical qualification. “If there’s an application that the financial department recently paid a lot of money for and bought a large number of licences, you can track whether it’s actually being used,” says Goldenberg. “If there’s an application you want to deprecate in your organisation because you decided to standardise on Office 365, you can check that the usage of alternatives that aren’t sanctioned — or that you want to stop paying for — is decreasing.”
SEE: 10 tricks and tweaks for customizing Windows 10 (free PDF) (TechRepublic)
Changing user behaviour takes more than blocking: you can also warn users so they understand the risk, and redirect them to a company portal listing preferred applications.
“We also have ‘break the glass [in emergency]’ scenarios where you can show the warning so users know this isn’t an application they should use, but they can click to confirm that they have a reason to use something the organisation does not recommend and then they have full access,” Goldenberg says. In future, that will include options to have employees provide a justification for why they need to use that cloud app, or to have their request sent to a manager for approval, with a portal where they can file access requests in advance. Goldenberg also suggests that access will get more granular in future — “It might be allowing limited access for so many minutes or so many days,” he says.
Coaching employees to use those apps is often more effective at a department level: admins can create PDF reports to send to managers showing how many cloud apps their teams are using, and how much data is going through them. You can also analyse the application usage data in Power BI.
Power BI reports let you see more detail or share trends without identifying users and devices.
” data-credit=”Image: Microsoft” rel=”noopener noreferrer nofollow”> Power BI reports let you see more detail or share trends without identifying users and devices. Image: Microsoft 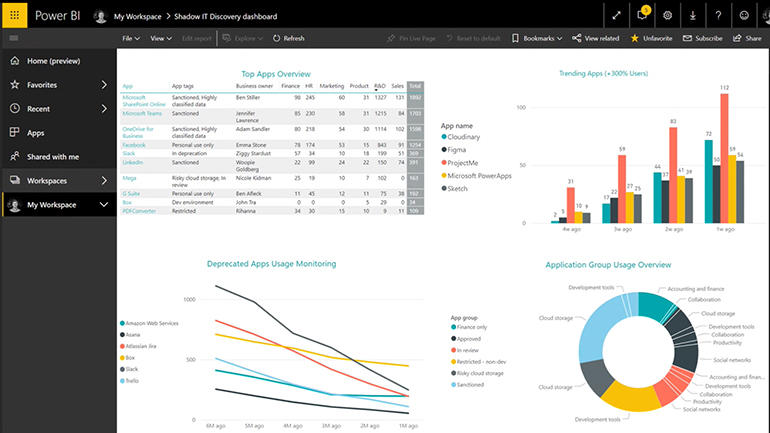
Collecting this much information about who uses what apps and opens which files could reveal quite a lot about your business, so all the data collected is encrypted and can be anonymised for employee privacy, with multiple roles depending on how much you want admins to see. “We provide the ability to anonymise the data and only de-anonymise it based on a specific business justification, and this is also audited,” Goldenberg says. You can also enable different levels of access in Power BI: a department manager might get to see which machines a particular cloud app is used on, but a firewall or network admin might only get high-level statistics about network usage.
The shadow IT tool is currently available for endpoints running Windows 10 1709 and later (although you’ll need to install an optional update on versions before 1903). It relies on the Defender agent, which Microsoft has already brought to Macs, and Mac support is on the roadmap. “This is security from Microsoft not for Microsoft, and we’ll be expanding these capabilities, as we expand Defender ATP to non-Windows devices,” Goldenberg says.
The same risk assessment is happening for the application marketplaces associated with Microsoft services. MCAS already rates all the applications in the Teams marketplace, and that’s being extended to other Microsoft application ecosystems like Office 365, because add-ons and plugins get access to the data in your tenant. That would give customers more confidence about adopting partner applications in Dynamics, and could be particularly useful if it’s extended to browser extensions for the new Edge.

Microsoft Weekly Newsletter
Be your company’s Microsoft insider with the help of these Windows and Office tutorials and our experts’ analyses of Microsoft’s enterprise products. Delivered Mondays and Wednesdays
